This post is based on the SQL query found here. It’s clearly a fairly niche requirement but it’s come in very handy.
Let me set the scene… An open Wi-Fi network is provided for a major public event but is only there for accredited users, not the general public, authenticated with a captive portal. Some members of the public will no doubt try connecting to the network, reach the CP and find they can’t get anywhere.
The problem is every connection consumes resources. If enough people do this there could be DHCP exhaustion and issues with the association table filling up. Assuming everything is sized appropriately it’s likely to be the number of associations that are the primary concern.
There are various answers this configuration, most of which revolve around better security in the first place, but there are good reasons it’s done this way… let’s move on.
MAC caching is being used by ClearPass so the logic says: “do I know this client and if so is the associated user account valid? If so return the happy user role, if not return the portal role”.
This means there are no auth failures – we’re never sending a reject, ClearPass returns the appropriate role.
What we want to do is identify clients that don’t go through captive portal authentication, and therefore just keep being given the portal role.
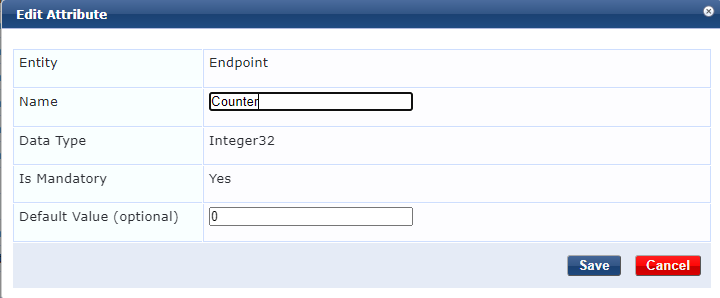
I added an Endpoint attribute of “Counter” (Administration\Dictionary Attributes)
Next a custom filter is added to the Endpoints Repository. This query (courtesy of the wonderful Herman Robers) reads the counter attribute into a variable of “Counter”. It also reads the counter attribute and adds 1 for the variable “Counter1”.
SELECT attributes->>'Counter' as Counter, (attributes->>'Counter')::int +1 as Counter1 FROM tips_endpoints WHERE mac_address = LOWER('%{Connection:Client-Mac-Address-NoDelim}')
Add this as an attributes filter under Authentication\Sources\Endpoints Repository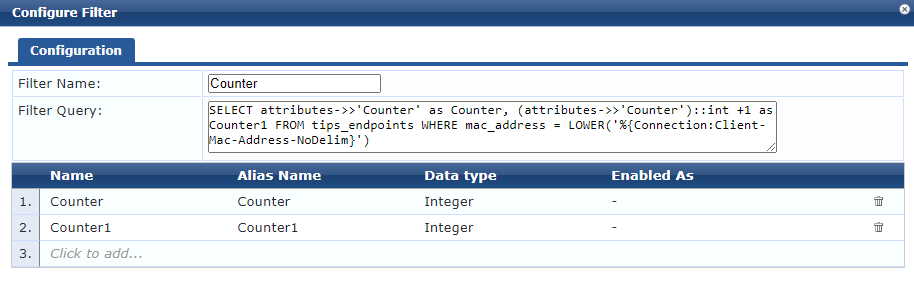
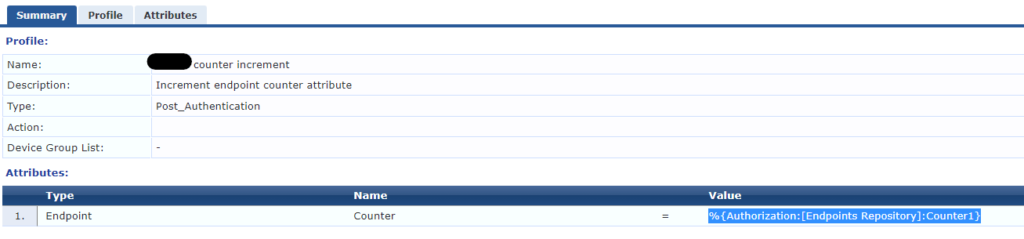
Within a Dot1X or MAC-auth service you can then call the variable: %{Authorization:[Endpoints Repository]:Counter1}
An enforcement profile is created to update the endpoint with the contents of Counter1 and this is applied alongside the portal role.
The result is each time a client hits the portal we also increment the counter number. At a threshold, to be determined by the environment, we start sending a deny. In my testing I set this to something like 5 to prove it worked.
This works well but a persistent client can just keep trying to connect which can still consume some resource as the AP has to generate auth traffic.
In this case the network is using Aruba Instant APs which have a dynamic denylist function. This was set to block clients for one hour after 2 authentication failures.
What happens now is after a client has hit the portal 5 times, ClearPass sends a reject, the client almost immediately tries again and is rejected, at which point it’s added to the denylist and can no longer associate with the network.
There are risks to this approach – it’s easy to see you could end up with false positives being denylisted. Clearly a better overall solution would be to avoid deploying an open network but that opens a whole other can of worms when dealing with a very large number of BYOD users.
